In this blog you’ll learn:
- Why government agencies, including law enforcement, keep failing on cloud security despite years of high‑profile breaches and compliance checklists.
- How misconfigurations, absent MFA, unpatched APIs, and ignored shared‑responsibility models expose both citizen data and agency‑run systems to attackers.
- What CISOs and senior leaders in these organizations should do next to treat cloud security as a governance and vendor‑management issue, not just a technical one.
In a previous article, I stressed that law enforcement and government agency leaders must first define their desired security posture, what acceptable risk looks like, how data must be protected, and what continuity standards are non-negotiable before sitting down with vendors to discuss solutions. Without clarity, conversations default to the vendors’ solution set, where their stack becomes your strategy by stealth.
Cloud and XaaS models can absolutely deliver on scale and modernization for government missions, but only if you enter those discussions grasping the full shared responsibility model and the bases providers aren’t always covering, as recent breaches prove.
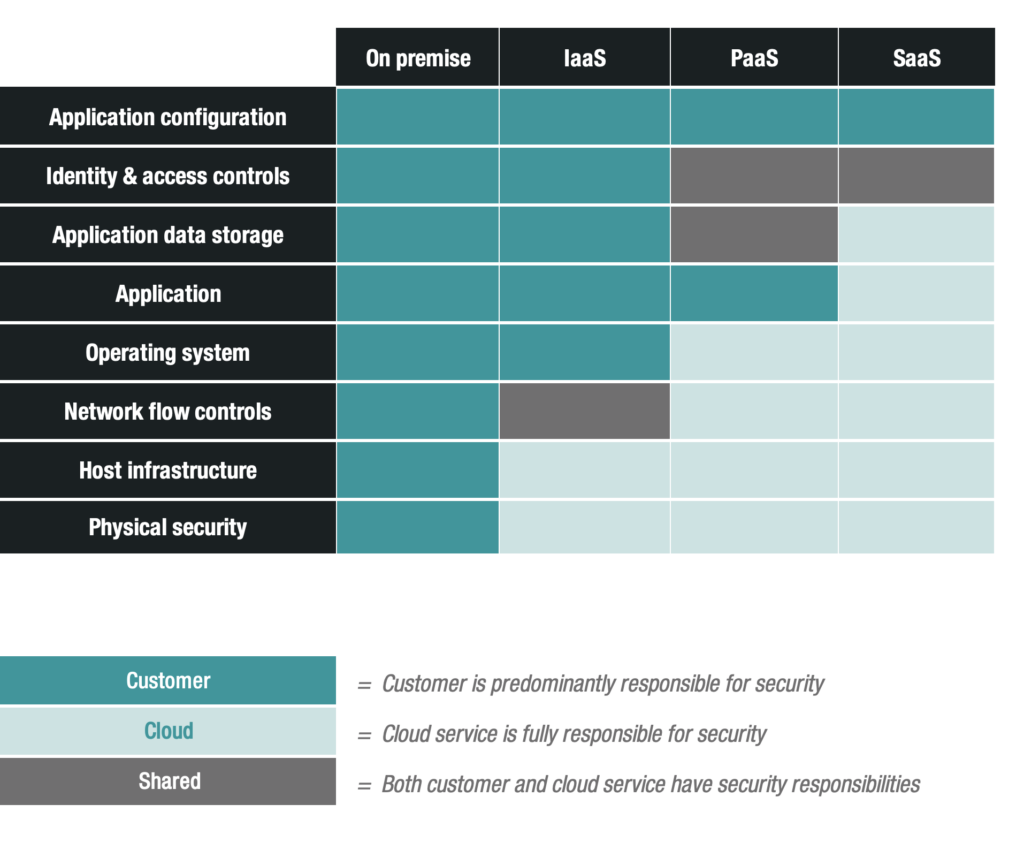
Shared responsibility model showing customer vs. provider security responsibilities across four deployment strategies. Adapted from the National Cyber Security Centre (NCSC), used under the Open Government Licence v3.0.
The Stubborn Vulnerabilities Agencies Keep Ignoring
Despite years of high-profile breaches and regulatory checklists, organizations handling critical data, especially governments and their vendors, continue to drop the ball on basic cloud protections. The recent Conduent ransomware attack, alongside Snowflake, Change Healthcare, and Ingram Micro incidents, lays bare the persistent gaps: misconfigurations, absent Multi-Factor Authentication (MFA), unpatched APIs, over-permissive Identity and Access Management (IAM), stale credentials, and ignored shared responsibility models that leave sensitive data dangling for attackers. We’re not getting this right because compliance often outweighs real security, vendor oversight is questionable, and the rush to scale via multi-cloud setups like Azure and Oracle Cloud Infrastructure (OCI) amplifies every weak link. While progress like FedRAMP expansions and CISA zero-trust adoption shows improvement, execution lags in complex supply chains.
The patterns are depressingly familiar; it’s the same playbook every time:
- Conduent’s SafePay ransomware lurked undetected from October 2024 to January 2025, siphoning 8 TB across hybrid clouds and exposing 25 million people’s SSNs, DOBs, addresses, medical data, and potential sensitive investigative records tied to state programs like child support enforcement or public safety processing.
- Snowflake’s 2024 UNC5537 crew waltzed in with stolen, unrotated credentials lacking MFA, hitting 165+ customers in both the private and public sectors.
- Change Healthcare’s BlackCat breach via a misconfigured Citrix portal in cloud-linked systems dumped 192.7 million health records.
- Ingram Micro lost 3.5 TB to similar SafePay tactics on unpatched APIs, reinforcing the same pattern of credential-based and misconfigured-API attacks.
These aren’t novel exploits; they were low-hanging fruit. Misconfigured IAM roles and excessive permissions continue to expose storage buckets. Unpatched APIs and remote access points without zero-trust enforcement let ransomware move laterally through systems. These risks are amplified when multi-cloud environments (such as Azure and OCI) aren’t unified. However, federal agencies adopting zero-trust principles, as recommended by CISA, can reduce the potential for lateral movement.
Shared responsibility gaps make matters worse. Many customers neglect their security obligations, skipping MFA or leaving credentials unchanged for years. These tendencies allow providers like Snowflake to deflect blame. Human error still accounts for roughly 26% of incidents, and about 99% of cloud failures stem from customer misconfigurations, according to IBM’s 2025 data. Yet despite these trends, we continue deploying large-scale Business Process and Customer Experience Services (BPaaS and CXaaS), compounding risk across millions of users without consistent enforcement.
Scaling Risk, Not Resilience
Texas and Oregon, with a combined 25.9 million residents affected, outsourced benefits, Medicaid, child support, and potentially investigative data handling to Conduent, only to see the breach persist for months. Follow-up investigations, including Texas AG probes and class actions, highlighted weak contracts, no mandated zero-trust controls, and no real-time vendor audits.
At the federal level, the picture is no more reassuring. FedRAMP enforces continuous monitoring for federal clouds but struggles with third-party supply chains, where agencies often rely on checkbox compliance rather than rigorous oversight.
Congressional hearings on the Change Healthcare breach revealed lapses like missing MFA on portals processing federal reimbursements. Separately, Snowflake credential theft, which hit several government-adjacent clients via stolen credentials, prompted CISA alerts. Despite CISA’s Zero Trust Maturity Model (ZTMM) guidance, federal responses remain reactive, defaulting to post-breach credit monitoring amid Conduent’s $25 million cleanup costs and broader trust erosion in critical sectors like health claims and emergency benefits.
Into 2026, the threat landscape continues to intensify. Zestix/Sentap campaigns are selling stolen ShareFile and Nextcloud credentials, often targeting government sectors through infostealer malware and absent MFA. Azure now accounts for 43.5% of cloud malware samples, non-human identities such as API keys are emerging as key vectors in AI-driven attacks, and CISA’s SCuBA baselines became mandatory for federal cloud tenants by mid-2025, requiring automated compliance checks to close gaps. Taken together, these signals point to a structural security problem unfolding in real time.
Supply Chain Fragility and Data Concentration
That problem is most visible in how modern cloud supply chains are designed. Conduent centralized multi-state data, turning one Safepay breach into a nationwide blast radius that evaded detection for three months despite scheduled audits and compliance certifications. Telecoms under CALEA offers a useful contrast: redundant, independent paths are built in specifically to preserve uptime for systems like 911. The lesson is that compliance alone does not prevent outages, resilience does. Cloud processors may satisfy similar checklist requirements, but they often skip endpoint defenses, AI anomaly detection, and real-time agency visibility into vendor telemetry, leaving agencies blind to lateral movement until exfiltration begins. In Conduent’s wake, states are demanding 24-hour breach notification SLAs. Even so, uneven enforcement continues to threaten GDPR-aligned data sovereignty in cross-border public safety sharing.
Vendor Lock-In and the Myth of Multi-Cloud Safety
But centralization isn’t the only source of risk. Multi-cloud sells resilience: Azure for contacts, OCI for tolling, and Google for eDiscovery. But it also fragments zero-trust controls, turning API gateways and service accounts into weak points across the vendor chain. Conduent’s BPaaS layers vendor risk on top of client clouds without baked-in CSPM scanning, allowing Safepay to persist through misconfigured IAM and shared storage. The result is the same risk pattern in a different package.
Vendor lock-in gets worse during provider switches. Rehosting toll data from OCI to AWS can trigger FedRAMP significant change notifications and reassessments that take months, while first-year migration costs are often 15 to 30 percent higher and cutovers carry disruption risk. States dependent on long-term toll processors like Conduent face similar problems, with contract dependencies making exit difficult even after incidents.
The deeper issue is that multi-cloud adoption at government scale has outpaced the security architecture needed to govern it.
ZTNA-style overlays could help bridge providers, but state-level adoption of Zero Trust still lags federal implementation significantly, leaving API attack surfaces exposed as infostealers continue to harvest stolen keys. Without unified overlays, expanding across vendors doesn’t distribute risk so much as multiply it.
The Human Cost: Real Risks to Real People
Tying these failures back to Conduent, Change, and Ingram, this is not abstract. Exposed SSNs fuel phishing campaigns, synthetic identities, and loan fraud. Health data enables medical identity theft and fake claims that leave victims fighting charges for years. Leaked investigative data can compromise ongoing cases, witness safety, and law enforcement operations if it is stored in breached government contractor systems. Financial data arms targeted scams. For vulnerable populations that rely on government services, including Medicaid enrollees and retirees, the result can be delayed benefits, shredded privacy, and long-term harms without meaningful recourse.
The damage doesn’t stop at stolen data. Ransomware encrypts operations entirely, Ingram’s $136 million daily loss being the clearest example, and the downstream effects cascade into public services that real people depend on.
Dark web dumps then extend the harm further, giving nation-states and criminals networks alike a ready inventory of exploitable records. With more than 25 million records exposed through Conduent alone, potentially the largest U.S. breach, scale transforms individual harm into systemic risk. These are ordinary people, not just elites, suffering because cloud-native hype continues to outrun basic security hygiene.
Breaking the Cycle: Time for Accountability, Not Just Checklists
Preventing the next breach starts with replacing compliance theater with enforceable accountability. FedRAMP and CISA guidelines exist, but execution lags. Governments must demand contractual zero-trust proofs, real-time telemetry sharing, and breach penalties—starting with mandatory right-to-audit clauses, standardized security annexes, and non-negotiables like IAM controls, logging, and backup/restore SLAs. Mandate MFA everywhere, automated config audits, and pen tests pre-deployment. Ditch vendor-blind trust; audit chains end-to-end. Train relentlessly on shared responsibility, because 99% customer failures won’t fix themselves.
Making Cloud Security Operational
These aren’t new revelations. NIST, CISA, and FedRAMP have waved these same red flags for years, yet they gather dust on shelves instead of driving action. Having the list doesn’t secure anything, leaders who execute on it separate the prepared from the perpetually breached. Here are a few ways to take meaningful action:
- CIOs/CISOs: Inventory all cloud vendors for MFA coverage, stale credentials, and logging gaps; run a tabletop on multi-vendor incident response. The key, fix what you find.
- Program Owners: Map data flows to identify concentration risks; define data minimization rules (e.g., tokenization) for sensitive PII/investigative records before the next RFP, and flag what stays on-premise.
- Procurement: Build a security annex template with zero-trust proofs, telemetry SLAs, and penalties; reject RFPs without it, no exceptions.
Until law enforcement and government leaders prioritize security over speed, treating sensitive data as a liability, not an asset, we’ll continue to cycle through megabreaches. Until cloud vendors and supply chains prove they can handle sensitive investigative data without three-month dwell times, on-premise retention for your highest-risk crown jewels may just remain the prudent default.
In the end, breaches don’t just annoy; they disrupt payments, enable ID theft, and fuel ransomware extortion. Agencies outsourcing critical functions owe better than reactive apologies and free credit freezes.
Get the basics right, or keep paying the price.